Introduction
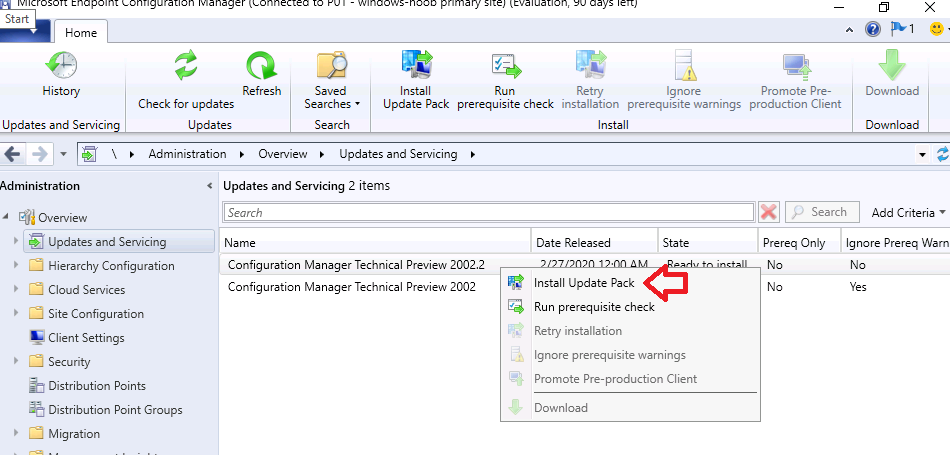
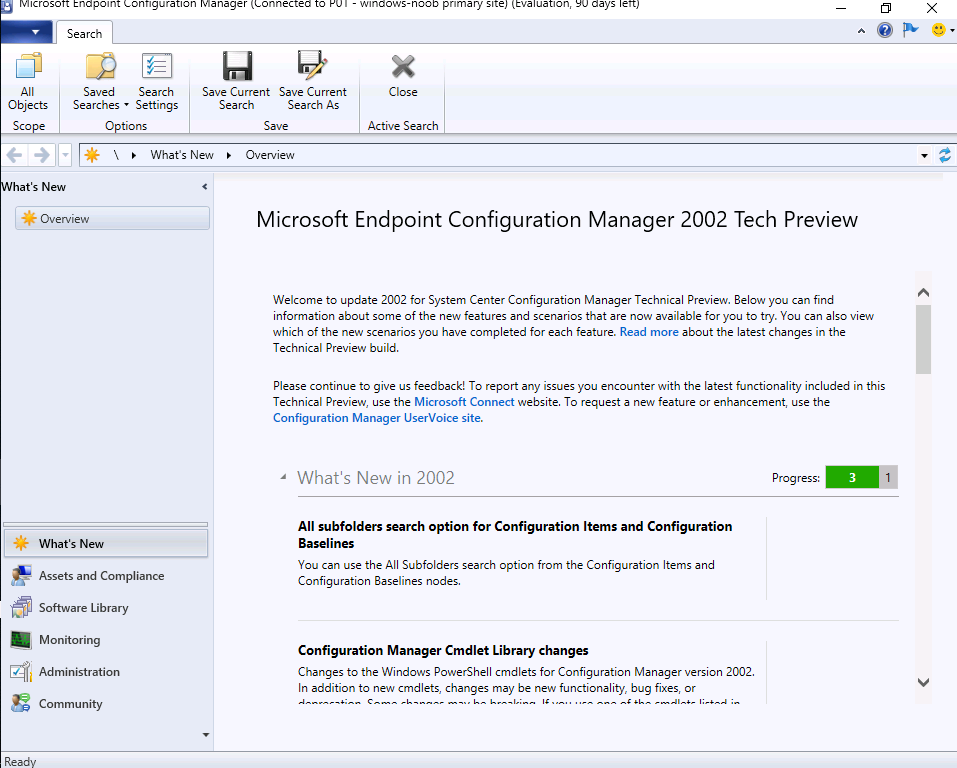
Microsoft have released the second update to Technical Preview this month, namely 2002.2.
 Below is a list of all the new features in this release.
Below is a list of all the new features in this release.
Management insight rules for proper HTTPS configuration
This release includes additional management insight rules to help you configure your site for secure HTTPS communication:
- Sites that don’t have proper HTTPS configuration: This rule lists sites in your hierarchy that’s not properly configured for HTTPS. This configuration prevents the site from synchronizing collection membership results to Azure Active Directory (Azure AD) groups. It may cause Azure AD sync to not upload all devices. Management of these clients may not function properly.
- Devices not uploaded to Azure AD: This rule lists devices that aren’t uploaded to Azure AD because the site isn’t properly configured for HTTPS.
For either rule, configure Enhanced HTTP, or enable at least one management point for HTTPS.
Note: Both rules did not appear in my TP lab, I believe that is because I’ve already configured mine for HTTPS communication.
Improvements to BitLocker management
In Configuration Manager current branch version 1910, to integrate the BitLocker recovery service you had to HTTPS-enable a management point. The HTTPS connection is necessary to encrypt the recovery keys across the network from the Configuration Manager client to the management point. Configuring the management point and all clients for HTTPS can be challenging for many customers.
Starting in this version, the HTTPS requirement is for the IIS website that hosts the recovery service, not the entire management point role. This change relaxes the certificate requirements, and still encrypts the recovery keys in transit.
Now the Client connections property of the management point can be HTTP or HTTPS. If the management point is configured for HTTP, to support the BitLocker recovery service:
- Acquire a server authentication certificate. Bind the certificate to the IIS website on the management point that hosts the BitLocker recovery service.
- Configure clients to trust the server authentication certificate. There are two methods to accomplish this trust:
- Use a certificate from a public and globally trusted certificate provider. For example, but not limited to, DigiCert, Thawte, or VeriSign. Windows clients include trusted root certificate authorities (CAs) from these providers. By using a server authentication certificate that’s issued by one of these providers, your clients should automatically trust it.
- Use a certificate issued by a CA from your organization’s public key infrastructure (PKI). Most PKI implementations add the trusted root CAs to Windows clients. For example, using Active Directory Certificate Services with group policy. If you issue the server authentication certificate from a CA that your clients don’t automatically trust, add the CA trusted root certificate to clients.
Tip
The only clients that need to communicate with the recovery service are those clients that you plan to target with a BitLocker management policy and includes a Client Management rule .
On the client, use the BitLockerManagementHandler.log to troubleshoot this connection. For connectivity to the recovery service, the log shows the URL that the client is using. Locate an entry that starts with Checking for Recovery Service at.
Improvements to support for ARM64 devices
This release improves upon the support for devices with the ARM64 processor. The All Windows 10 (ARM64) platform is now available in the list of supported OS versions on the following objects:
- Configuration item supported platforms
- Application deployment type requirements
- Package program requirements
- Task sequence advanced properties
Note
If you previously selected the top-level Windows 10 platform, this action automatically selected both All Windows 10 (64-bit) and All Windows 10 (32-bit). This new platform isn’t automatically selected. If you want to add All Windows 10 (ARM64), manually select it in the list.
For more information on Configuration Manager’s support for ARM64 devices, see Windows 10 on ARM64.
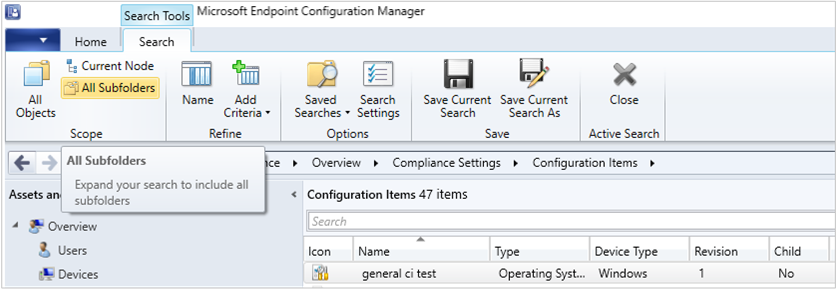
Search all subfolders for configuration items and configuration baselines
Similar to improvements in previous releases, you can now use the All Subfolders search option from the Configuration Items and Configuration Baselines nodes.
Support for 64-bit macOS Catalina
Configuration Manager now supports the 64-bit macOS Catalina version 10.15. For more information, see the following articles:
- Supported OS versions for clients and devices
- Download Microsoft Endpoint Configuration Manager – macOS Client (64-bit)
You can also use the Intune cloud service for managing macOS devices. For more information, see Set up enrollment for macOS devices in Intune.
Improvements to extend and migrate on-premises site to Microsoft Azure
Extend and migrate on-premises site to Microsoft Azure now supports provisioning multiple site system roles on a single Azure virtual machine. You can add site system roles after the initial Azure virtual machine deployment has completed. To add a new role to an existing virtual machine, do the following steps:
- On the Deployments in Azure tab, click on a virtual machine deployment that has a Completed status.
- Click the Create new button to add an additional role to the virtual machine.
Microsoft Endpoint Configuration Manager cloud features
When new cloud-based features are available in the Microsoft Endpoint Manager admin center, or other attached cloud services for your on-premises Configuration Manager installation, you can now opt in to these new features in the Configuration Manager console. For more information on enabling features in the Configuration Manager console, see Enable optional features from updates.



Pingback: Using the new Tenant Attach feature in Configuration Manager TP2002.2 | just another windows noob ?